If your Pelican-generated site uses lots of different tags for articles, it can
be difficult to remember or use tag names consistently. Therefore I needed a
quick method to print (comma separated) unique tags that were stored in text
files.
This shell one-liner from within the content directory will sort and show all
tags from reStructuredText (
*.rst
) files:
grep -h '^:tags:' *.rst | sed -e 's/^:tags:\s*//;s/\s*,\s*/\n/g' | sort -u
First
grep
will filter on the
:tags:
property and will only
print out the matching line (without filename, thanks to the -h flag).
Then
sed
will remove the
:tags:
keyword (and trailing spaces),
and all tags will be split using newline characters.
Finally,
sort
takes care of sorting and only printing unique entries.
Analogous, one can do the same for categories:
grep -h '^:category:' *.rst | sed -e 's/^:category:\s*//' | sort -u
As Pelican only allows one category, this is somewhat simpler.
For maximum readability,
tr
can convert the newlines into spaces, so
that the output is one big line:
grep -h '^:tags:' *.rst | sed -e 's/^:tags:\s*//;s/\s*,\s*/\n/g' | sort -u | tr '\n' ' '; echo
The last echo is meant to end …
more ...
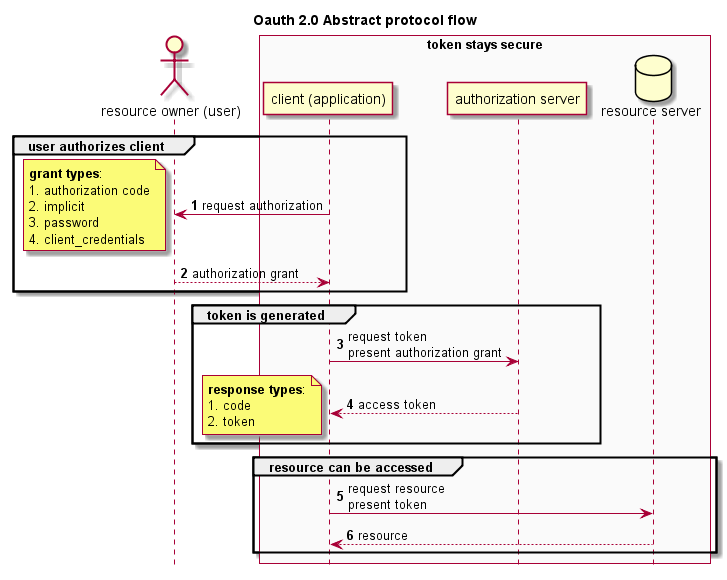
 Researching new vulnerabilities, techniques or concepts can be
time-consuming and sometimes chaotic. A streamlined workflow is
necessary to make the process as efficient as possible. This article
describes the open source tools and well-known standards that I'm
currently using for that purpose.
Researching new vulnerabilities, techniques or concepts can be
time-consuming and sometimes chaotic. A streamlined workflow is
necessary to make the process as efficient as possible. This article
describes the open source tools and well-known standards that I'm
currently using for that purpose.